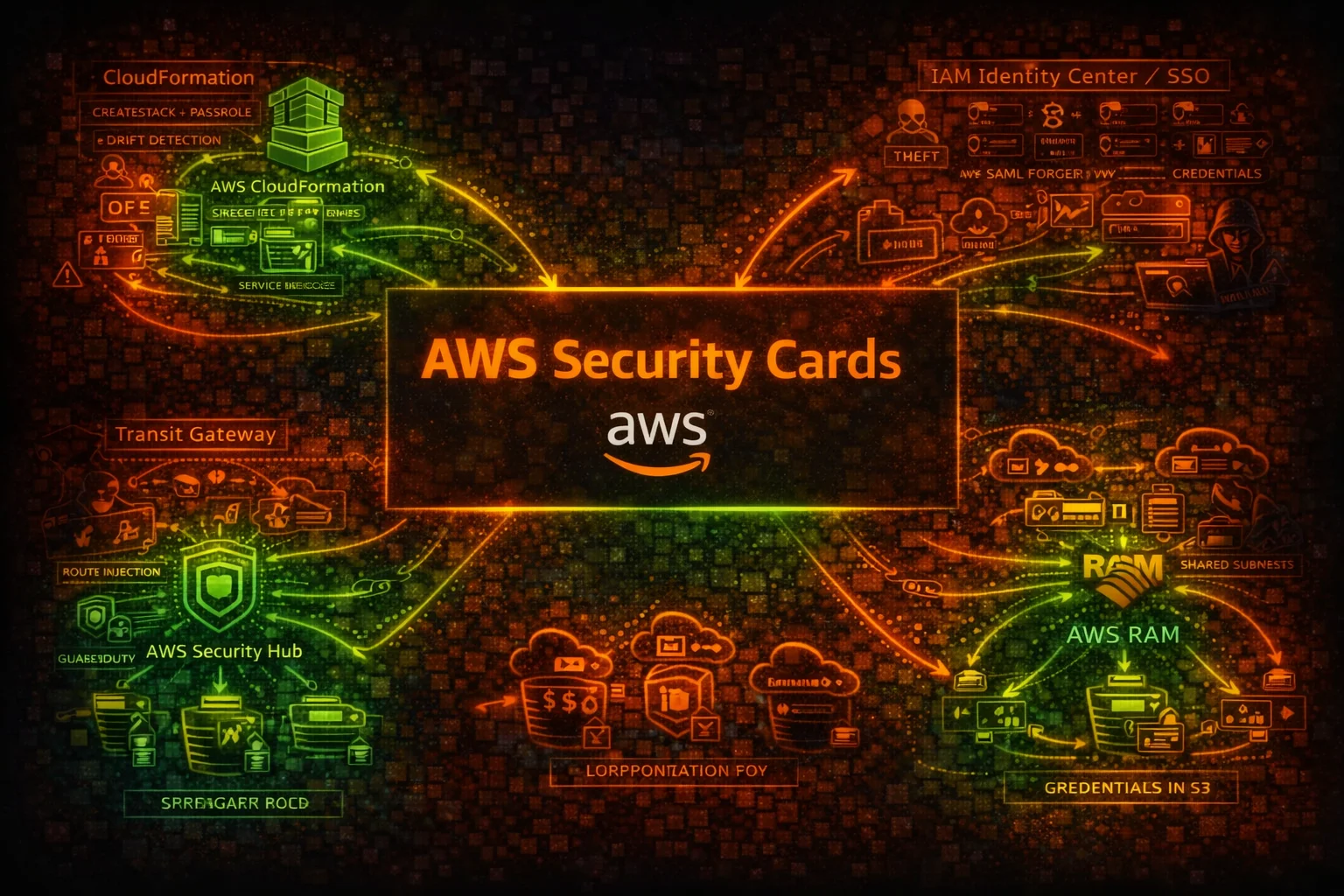
AWS Security Cards: Free Offensive Security Reference for 60 AWS Services
Tarek Cheikh
Founder & AWS Cloud Architect
AWS documentation tells you how services work. It doesn't tell you how they break.
AWS Security Cards: fills that gap. It's a free, open-source set of security reference cards: one per AWS service, 60 total, covering attack vectors, misconfigurations, enumeration commands, privilege escalation, persistence, detection, and defense. Available in Markdown, HTML, and PDF.
What's in a card

Each card covers a single AWS service from an offensive and defensive security perspective:
- Service overview: with attacker-relevant context
- Attack vectors: concrete exploitation paths, not vague risk statements
- Common misconfigurations: what actually leads to breaches
- Enumeration commands: copy-paste AWS CLI for security assessments
- Privilege escalation: how read access becomes admin
- Persistence techniques: how access survives incident response
- Detection indicators: what shows up in CloudTrail and monitoring
- Policy examples: good vs. bad IAM/resource policies, side by side
- Defense recommendations: hardening commands you can run today
- Risk score: from 5.5 to 9.5, to help prioritize
Risk scores across the board
| Risk | Services |
|---|---|
| 9.5 | IAM, STS, Organizations, Secrets Manager, Identity Center |
| 9.0-9.2 | Redshift, EC2, S3, EKS, RDS, CodeBuild, CloudFormation, Route 53, Backup, Glue, Directory Service |
| 8.5 | CloudTrail, API Gateway, ECR, ECS, OpenSearch, Systems Manager, SageMaker, Step Functions, Security Hub, Transit Gateway |
| 7.0-8.0 | DynamoDB, Cognito, KMS, EBS, AppSync, Athena, EventBridge, RAM, VPC, GuardDuty, and more |
| < 7.0 | App Runner, SQS, ELB, SNS, Amplify, Inspector, ACM, Network Firewall, WAF |
Some of these might surprise you. AWS Backup at 9.0, higher than Lambda. An attacker who gets into Backup can delete every recovery point in your account. Ransomware with no recovery path. CodeBuild at 9.0, one malicious buildspec exfiltrates every secret and poisons every artifact downstream.
A few things worth knowing
There are 20+ known privilege escalation paths through IAM alone. CreatePolicyVersion, PassRole, UpdateAssumeRolePolicy, AttachUserPolicy. Most AWS accounts have at least one of these unguarded.
Many persistence techniques don't produce obvious CloudTrail signals. A Lambda layer with a backdoor, an ECR image with a modified entrypoint, a trust policy added to a role. Standard alerting won't catch these unless you're specifically looking.
CI/CD is the new perimeter. ECR, CodeBuild, and CodePipeline are supply chain components. Compromise one, and everything that deploys through it is tainted.
Formats
Each card ships in three formats, all generated from the same source:
- Markdown: readable on GitHub, easy to search and contribute to
- HTML: standalone dark-themed pages, works offline in any browser
- PDF: print-ready, with embedded images and AWS service icons
Use cases
Print the PDFs for your next pentest. Use the enumeration commands during a security assessment. Hand the defense recommendations to your engineering team after an audit. Use the policy examples in a training session. Search the Markdown files when you need to quickly check a specific service.
Contribute
MIT licensed. If something is wrong or missing, open a PR.
Go Deeper: The State of AWS Security 2026
This article is just the start. Get the full picture with our free whitepaper - 8 chapters covering IAM, S3, VPC, monitoring, agentic AI security, compliance, and a prioritized action plan with 50+ CLI commands.
More Articles
Run AI Locally for AWS Security Work: The Complete Ollama Guide
Stop sending your IAM policies, CloudTrail logs, and infrastructure code to third-party APIs. Run LLMs locally with Ollama on Apple Silicon: private, offline, fast. Complete setup guide with AWS security use cases.
We Detonated the Real LiteLLM Malware on EC2: Here's What Happened
We obtained the actual compromised litellm packages, set up a disposable EC2 instance with honeypot credentials and mitmproxy, and detonated the malware. Full evidence: fork bomb, credential theft in under 2 seconds, IMDS queries, AWS API calls, and C2 exfiltration.
Anatomy of a Supply Chain Attack: How LiteLLM Was Weaponized in 6 Hours
A deep technical breakdown of how threat actor TeamPCP compromised Trivy, pivoted to LiteLLM, and turned a popular AI proxy into a credential-stealing weapon targeting AWS IMDS, Secrets Manager, and Kubernetes.