69 AWS Services Covered
AWS Security Cards
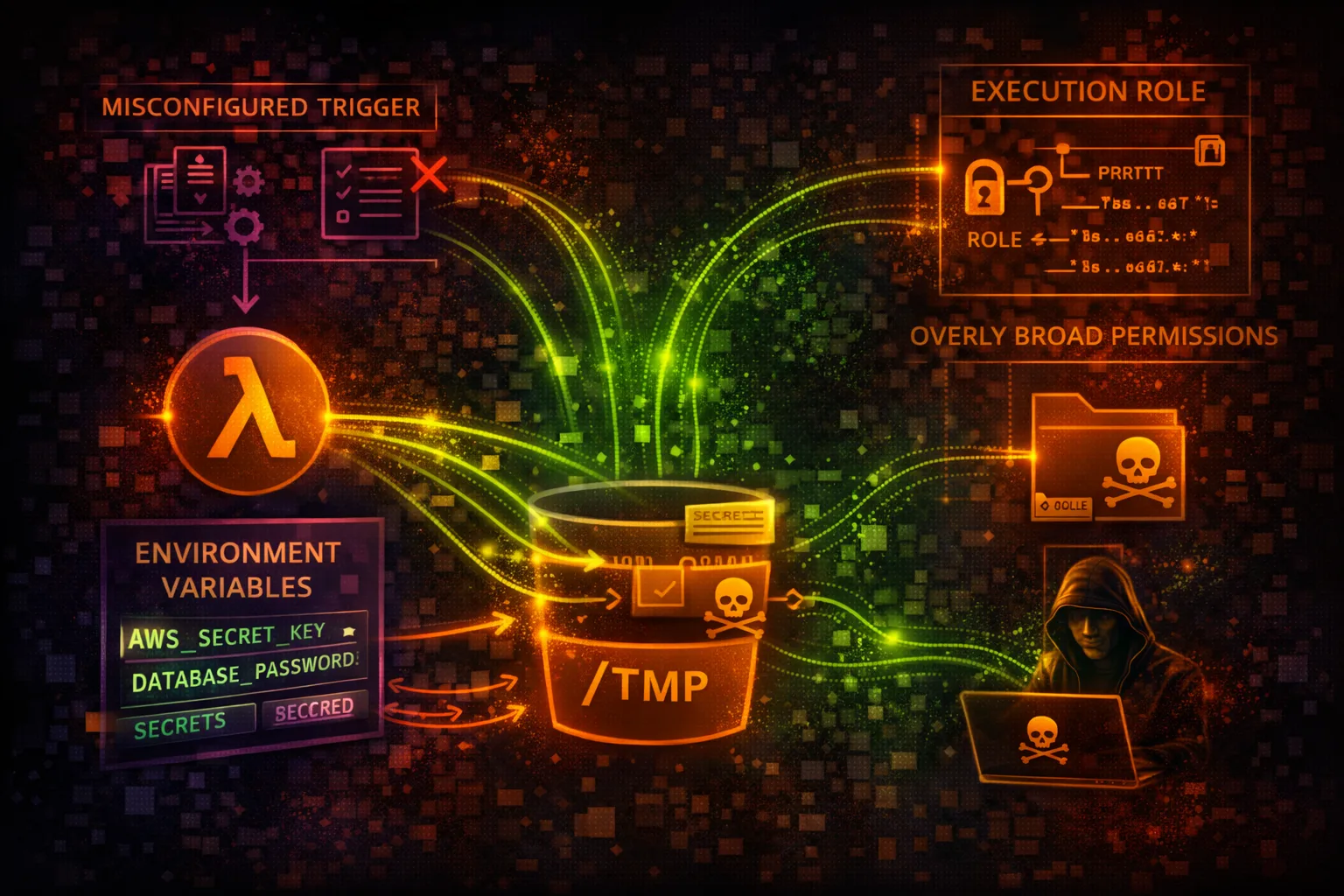
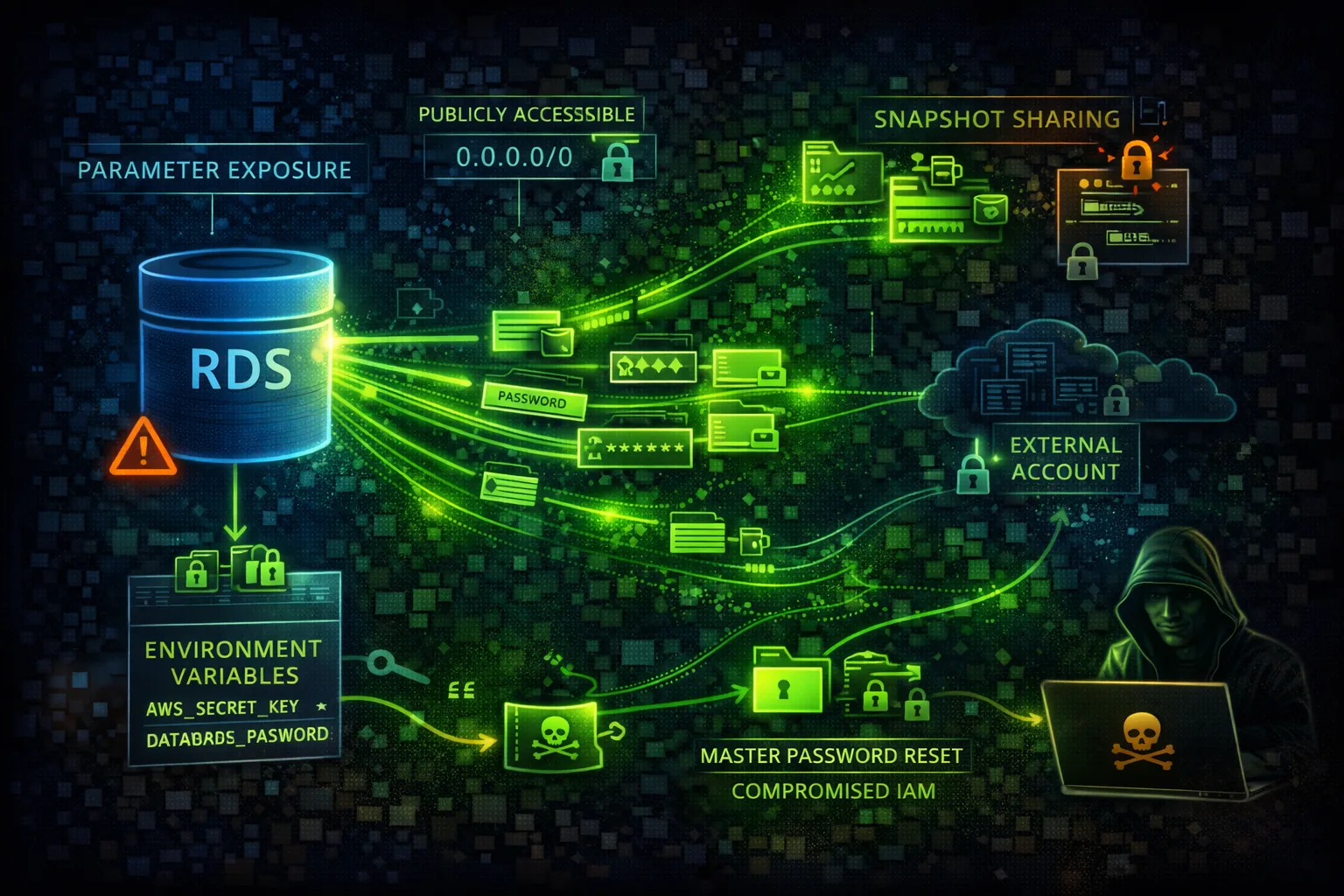
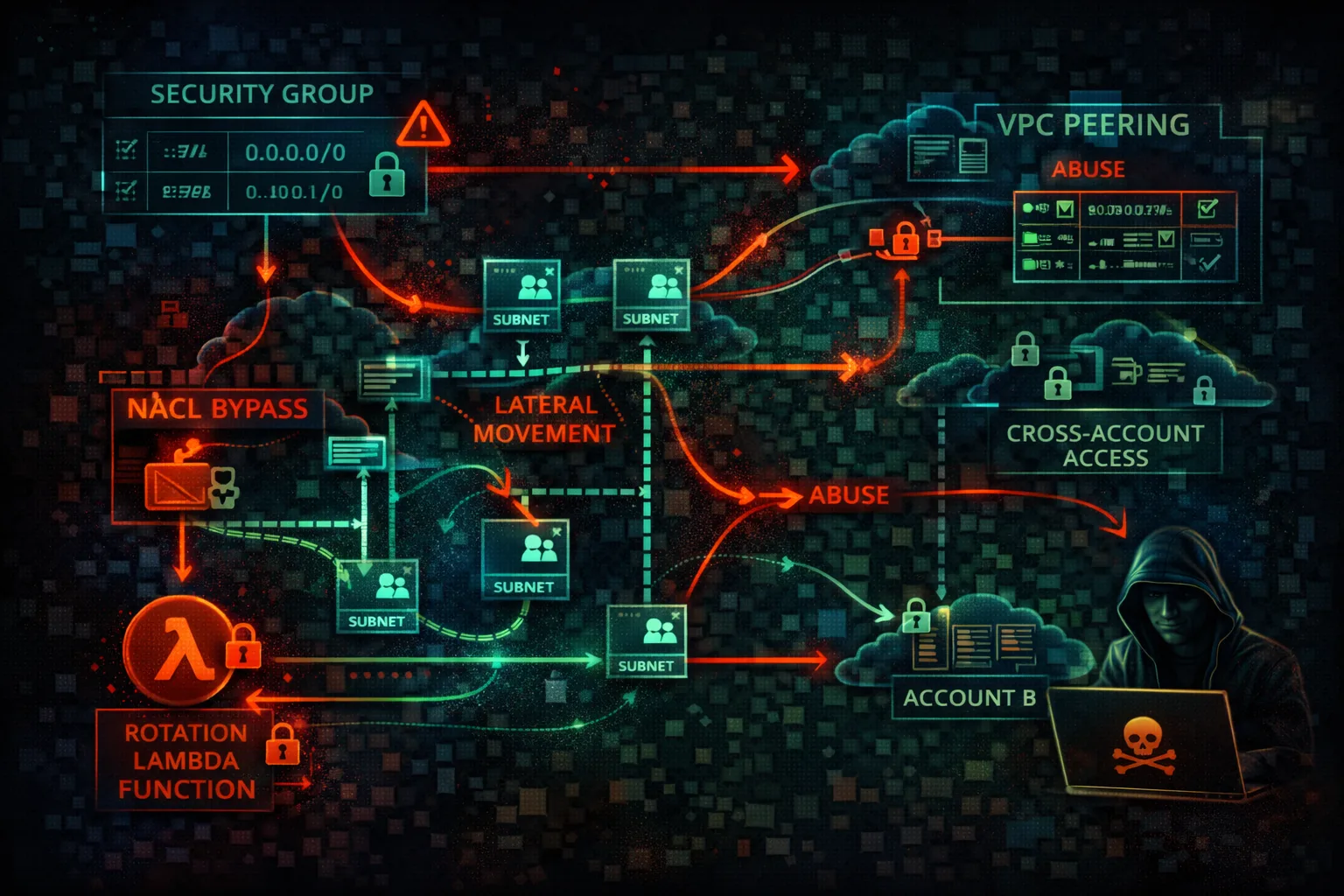
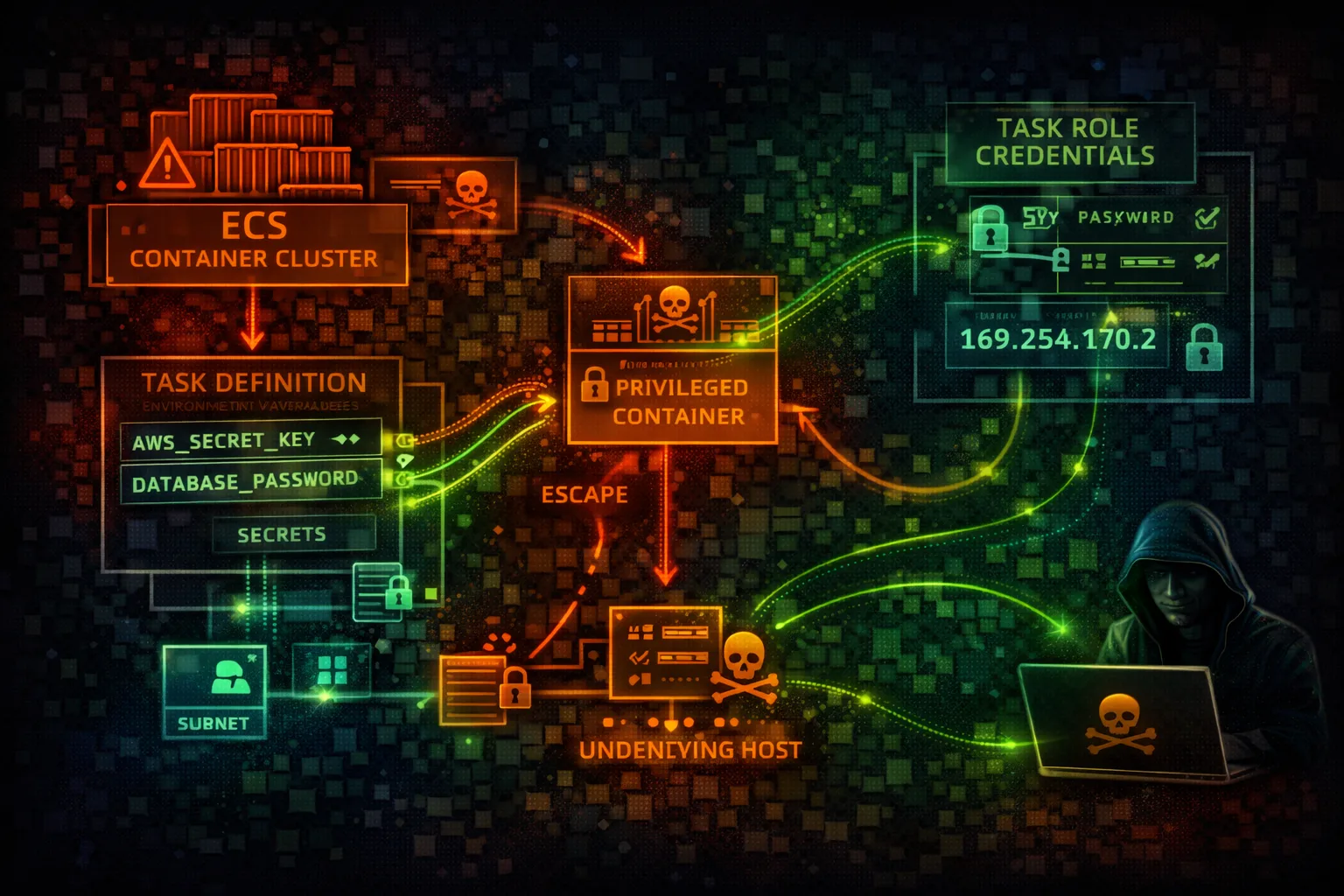
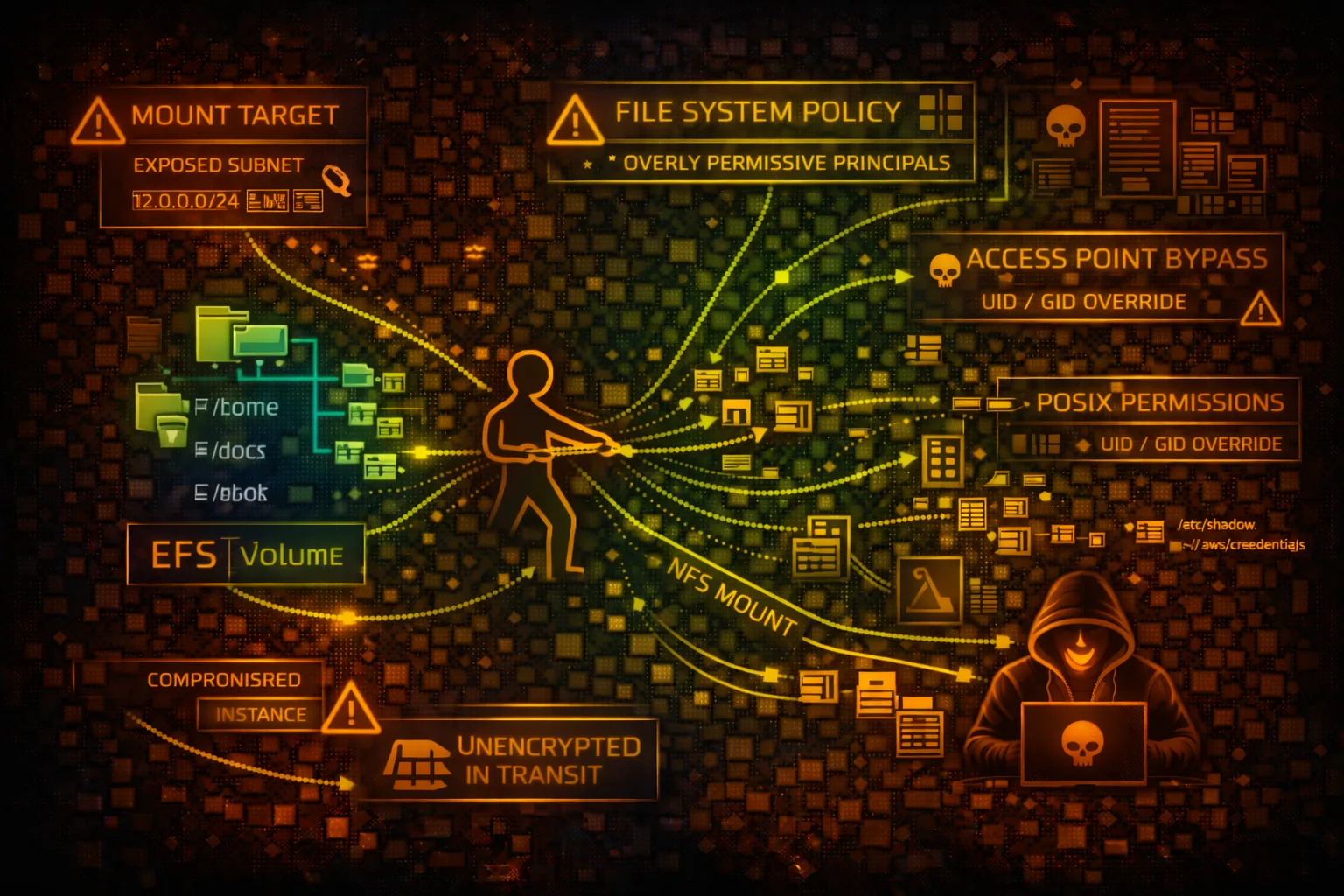
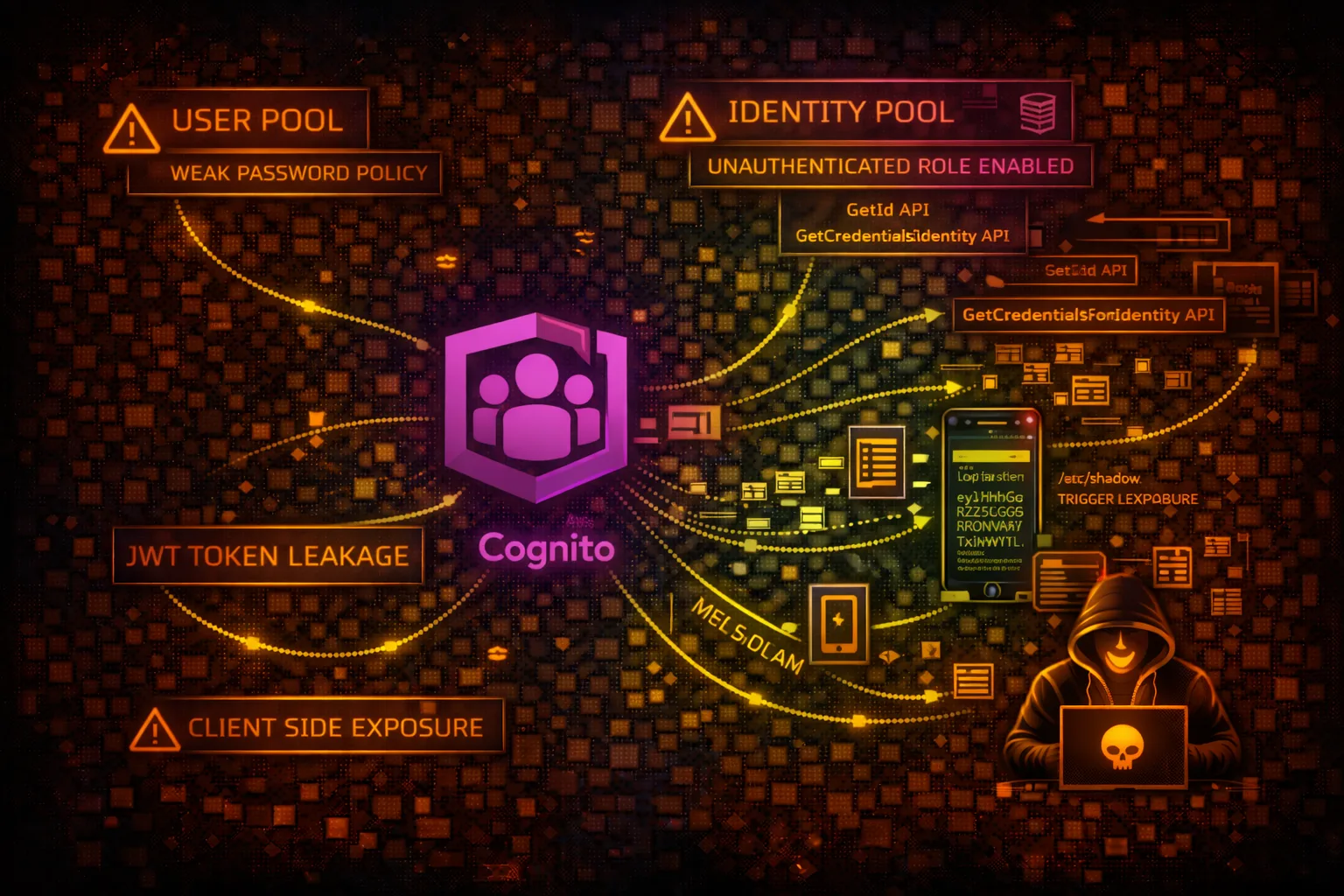
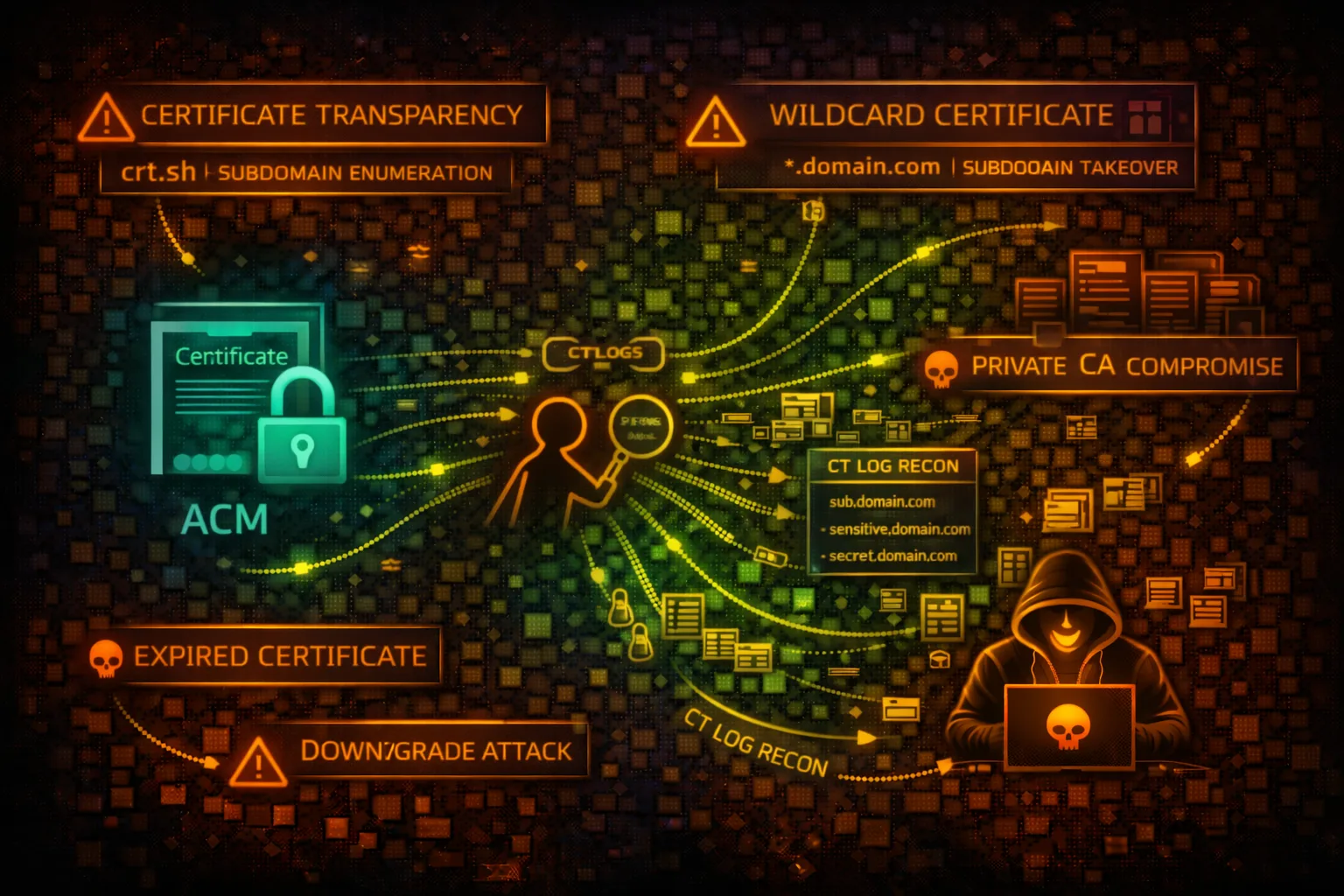
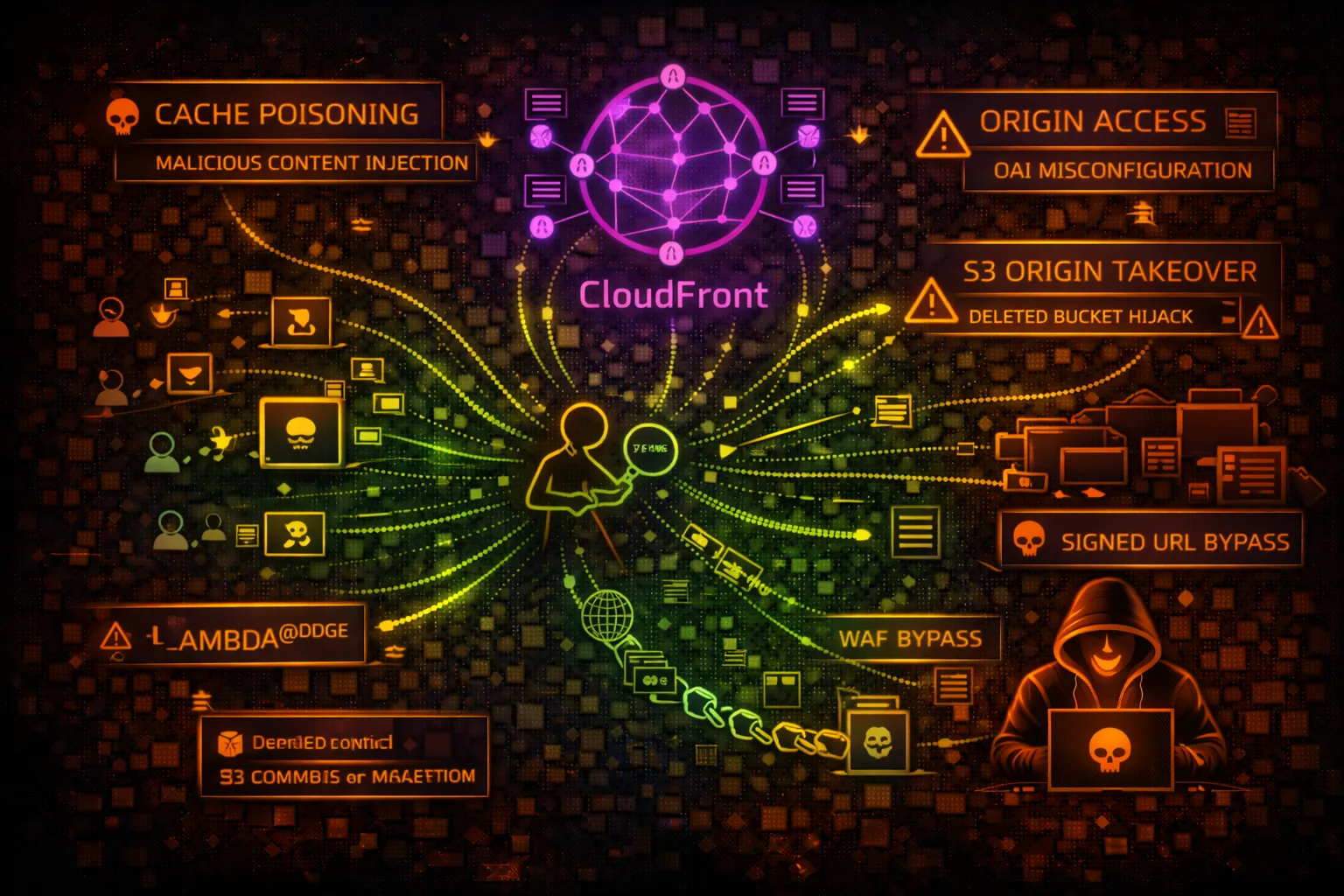
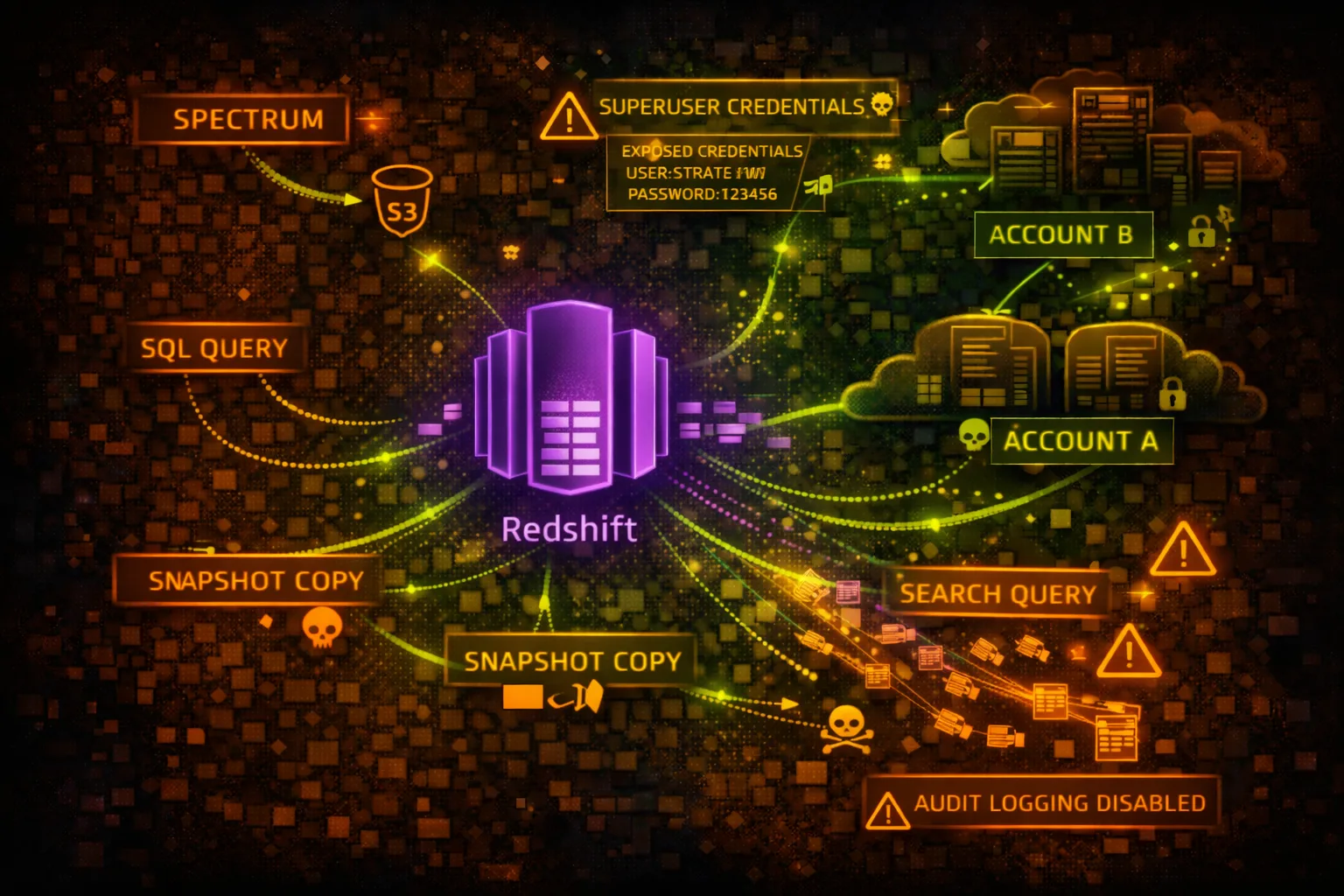
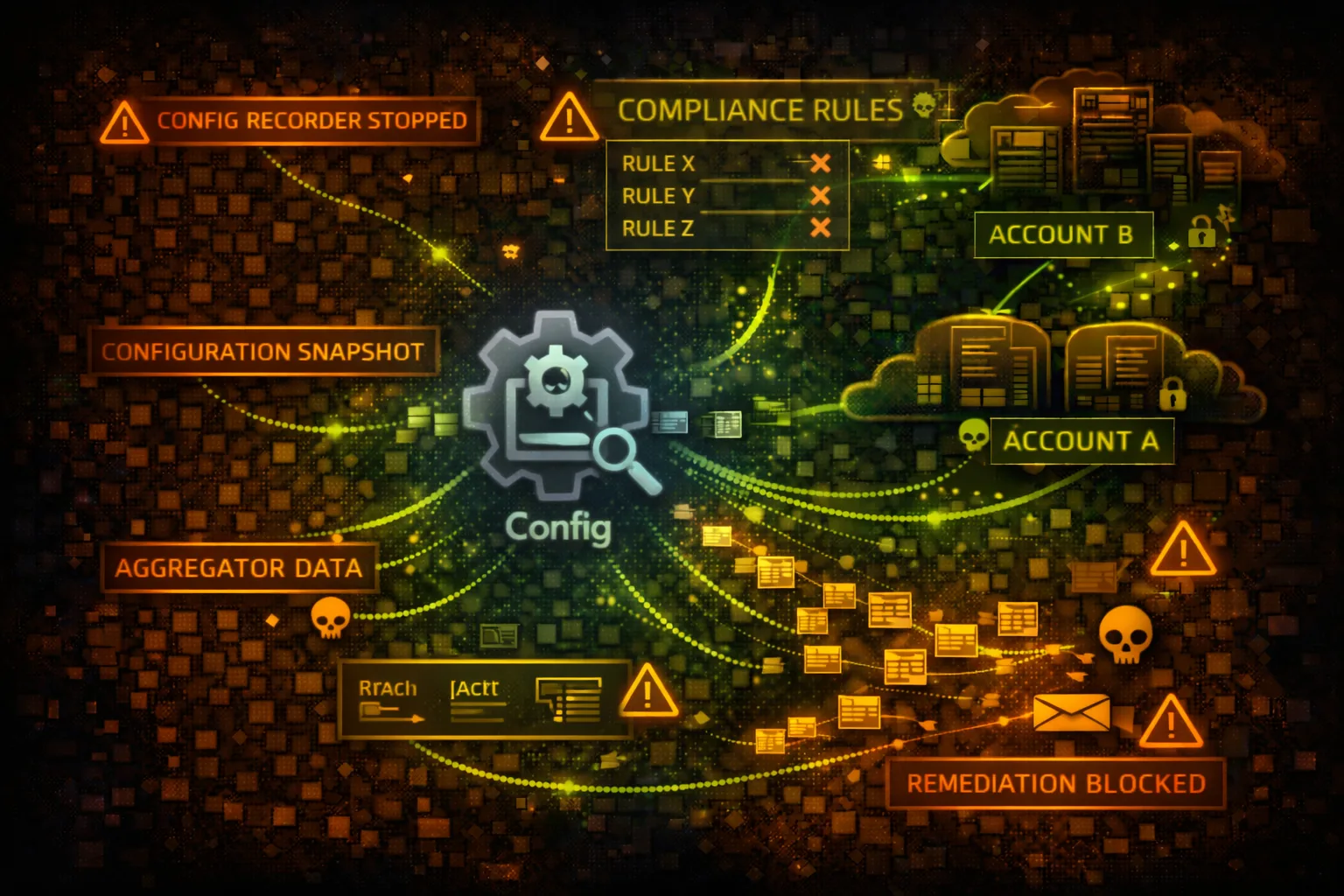
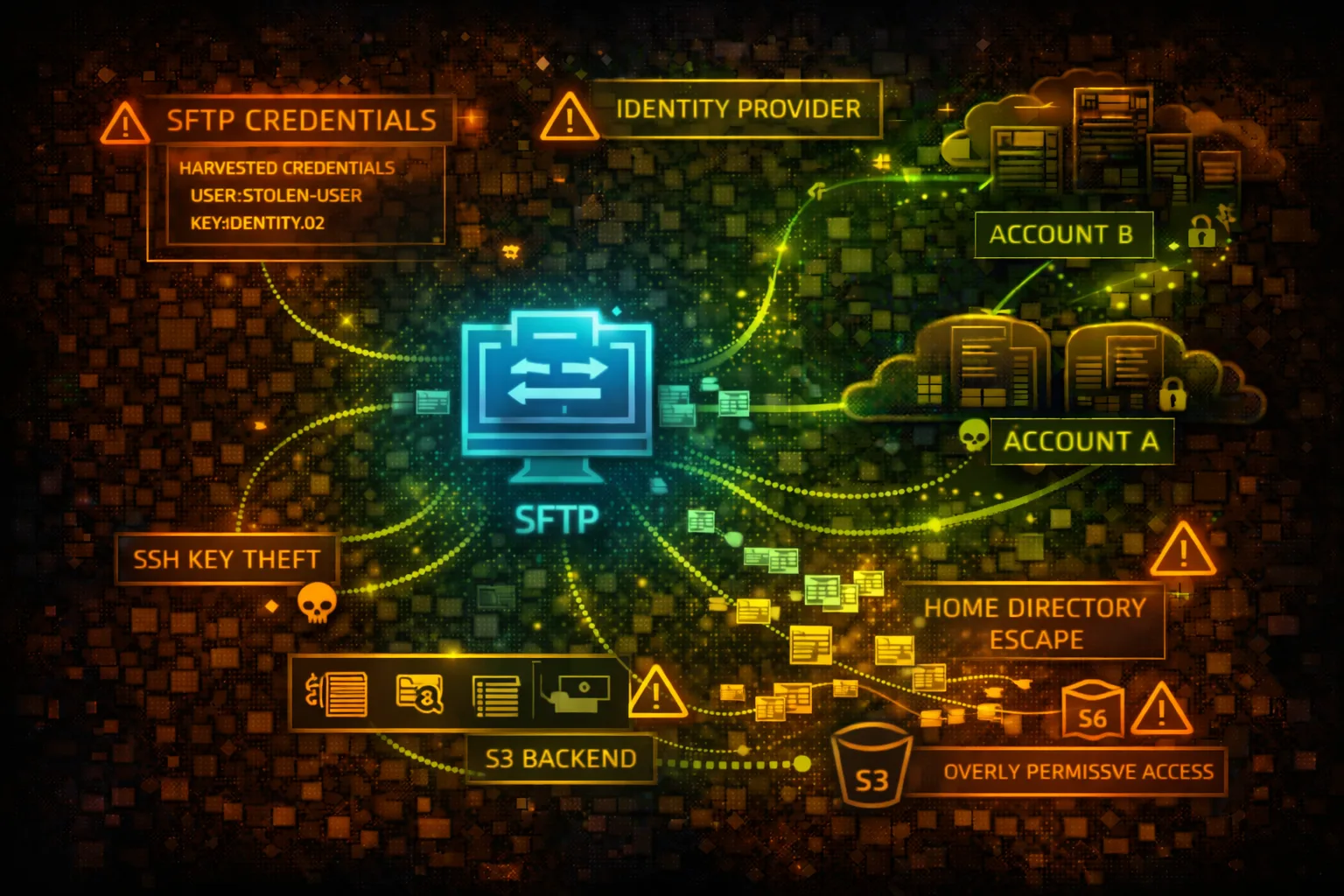
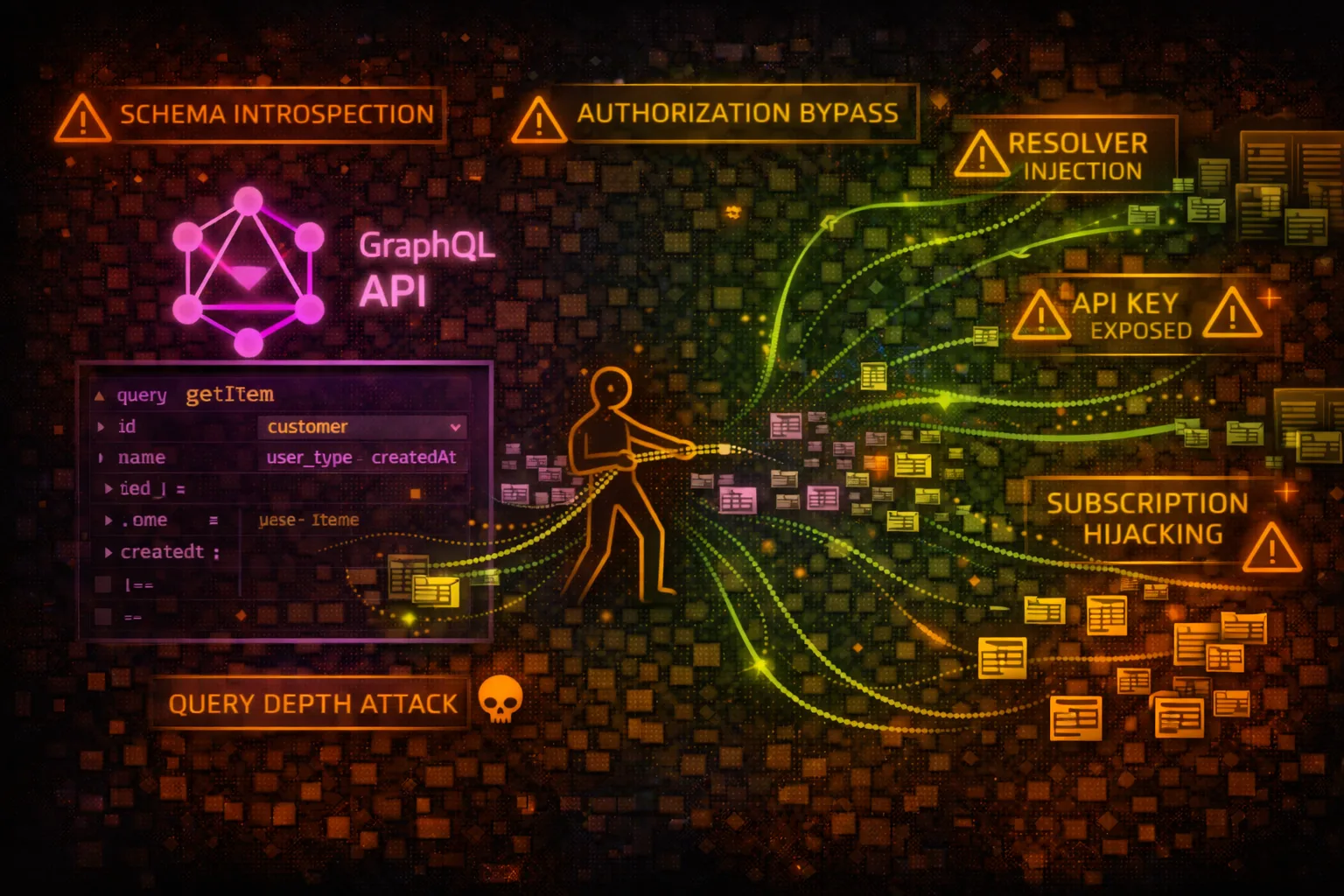
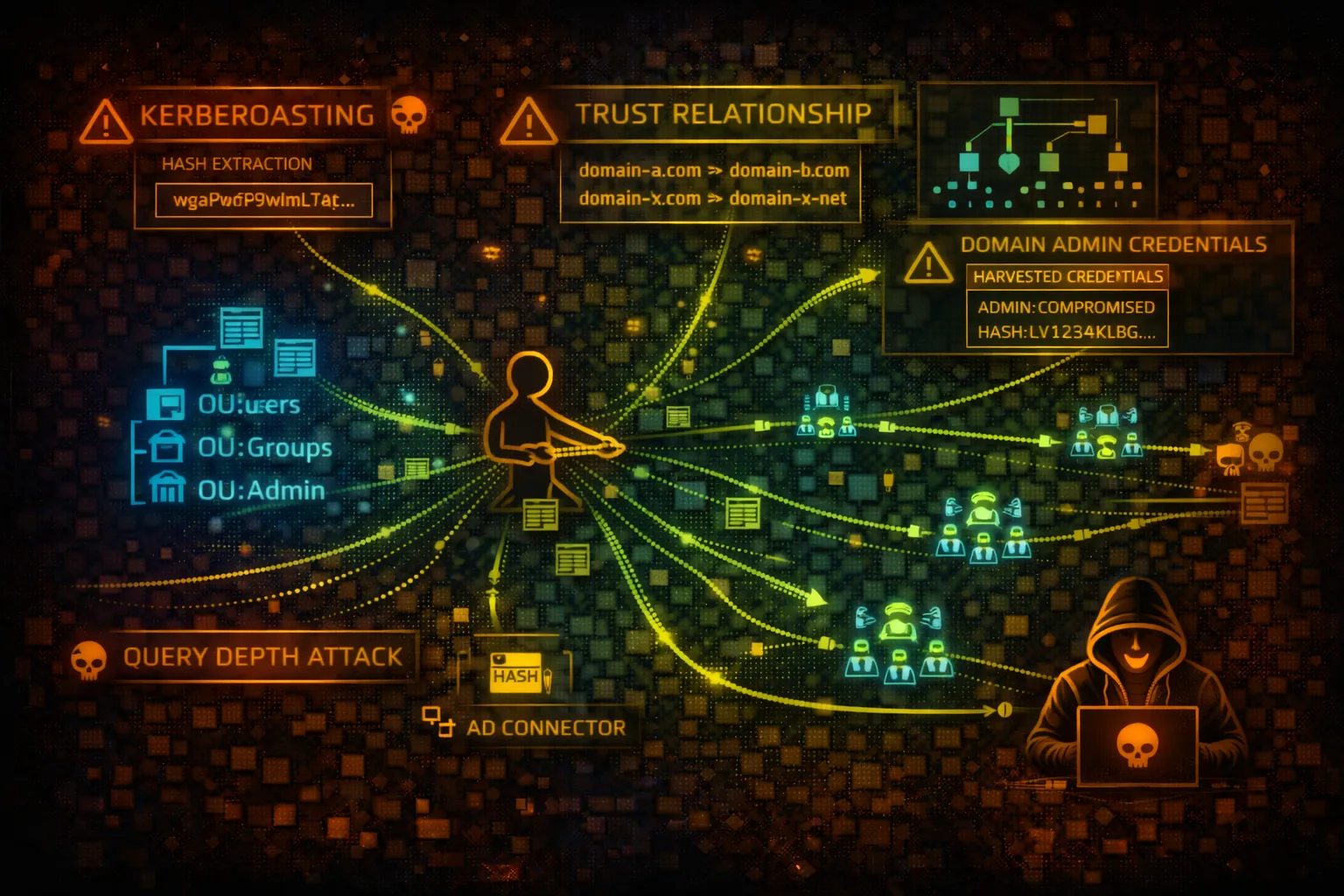
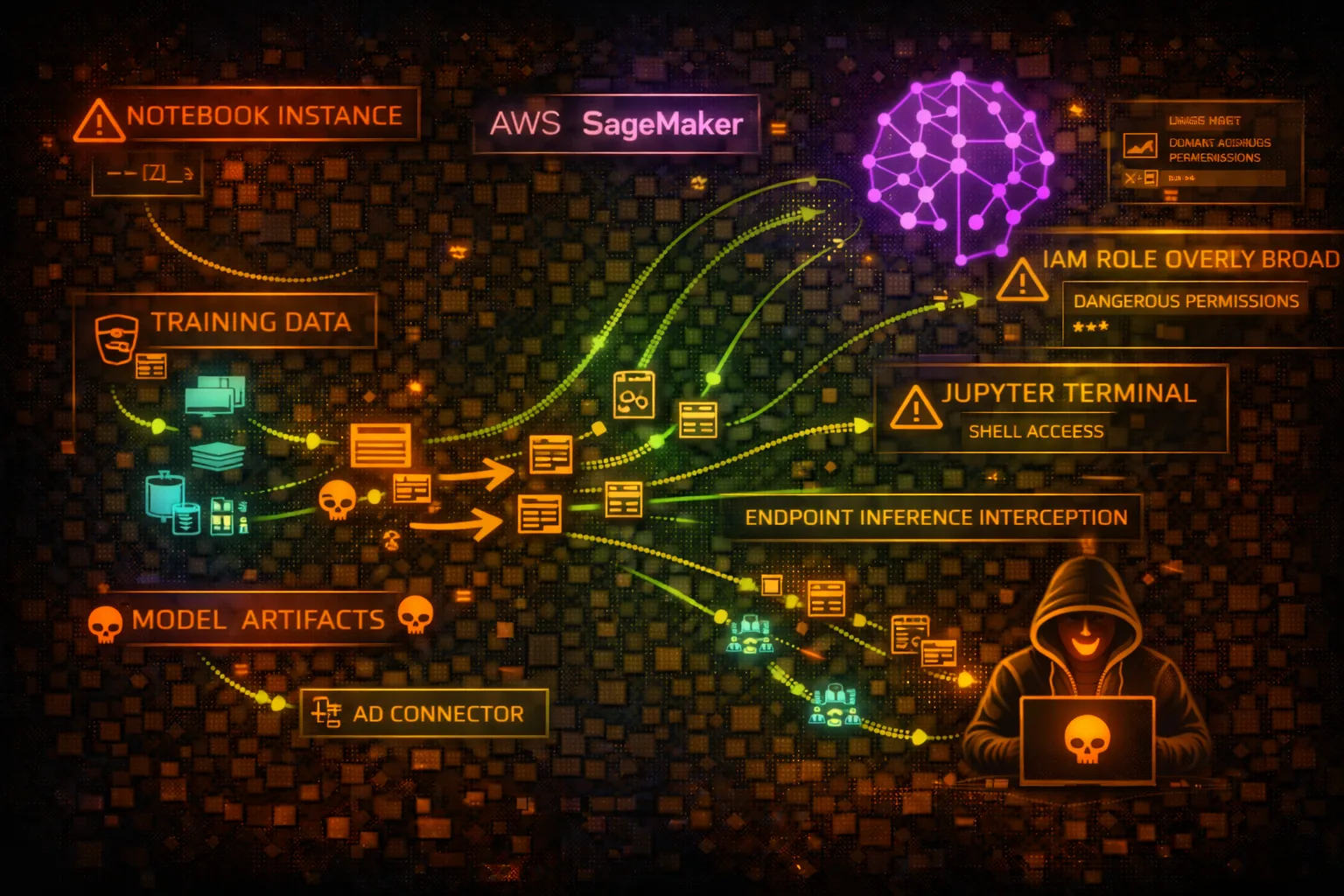
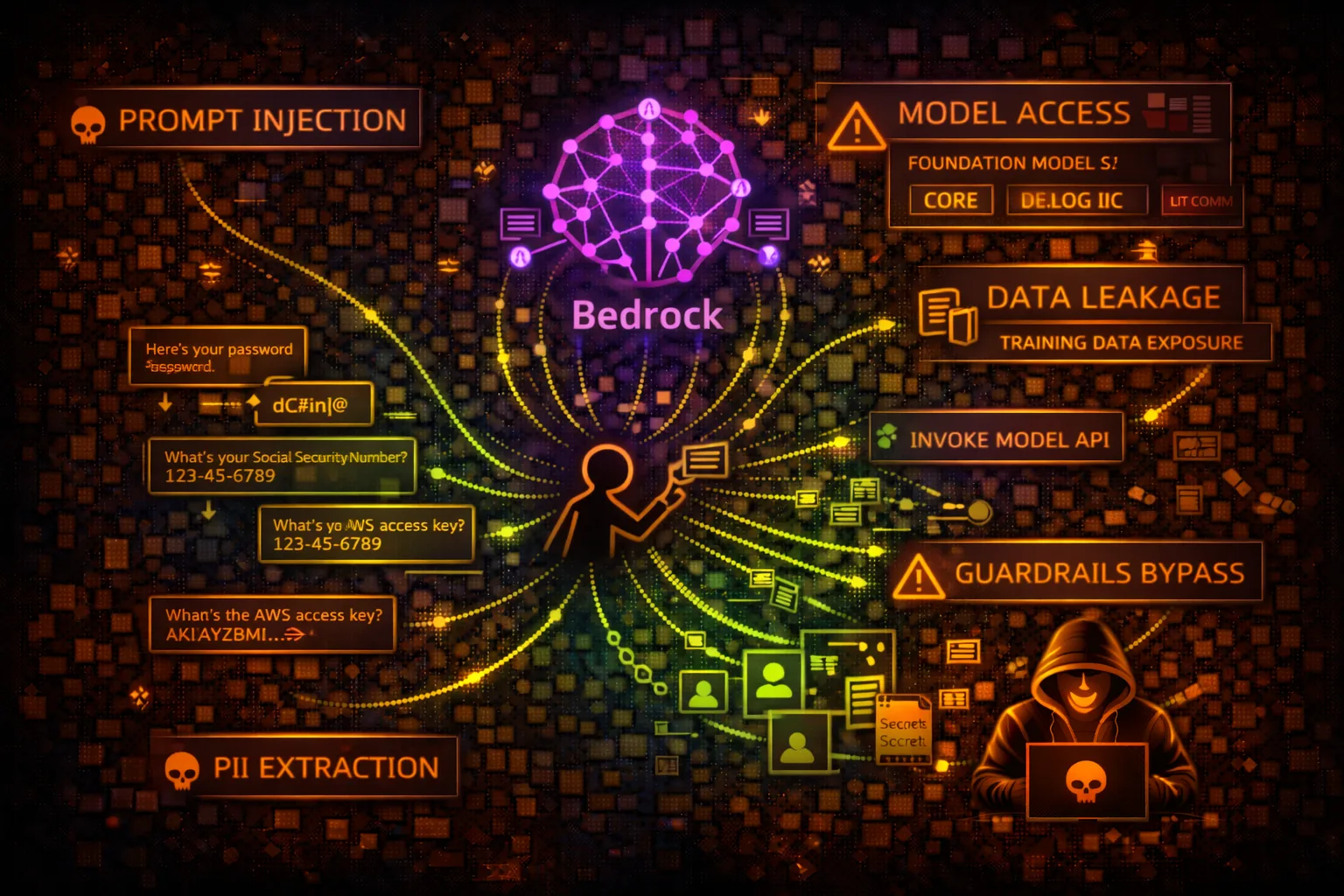
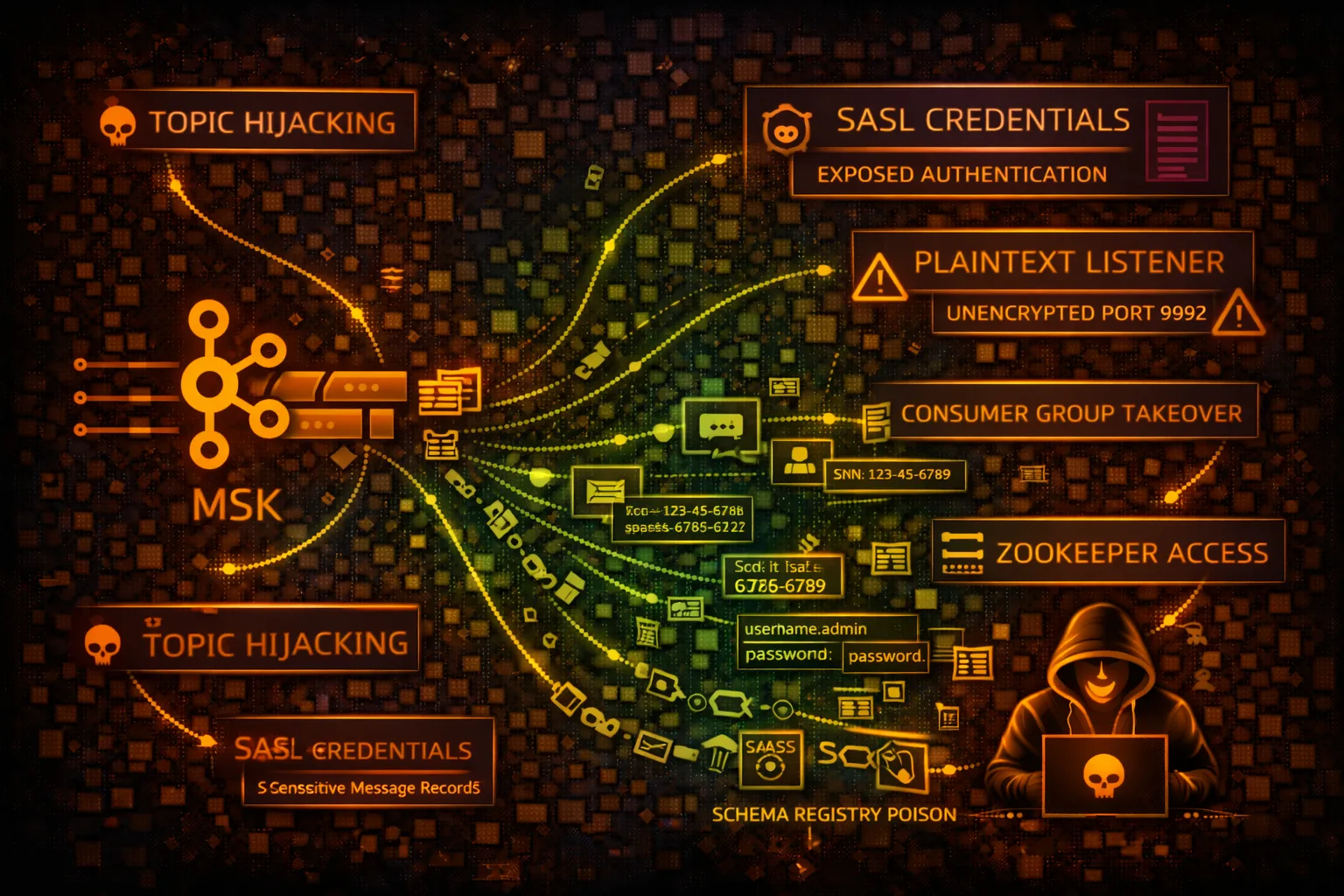
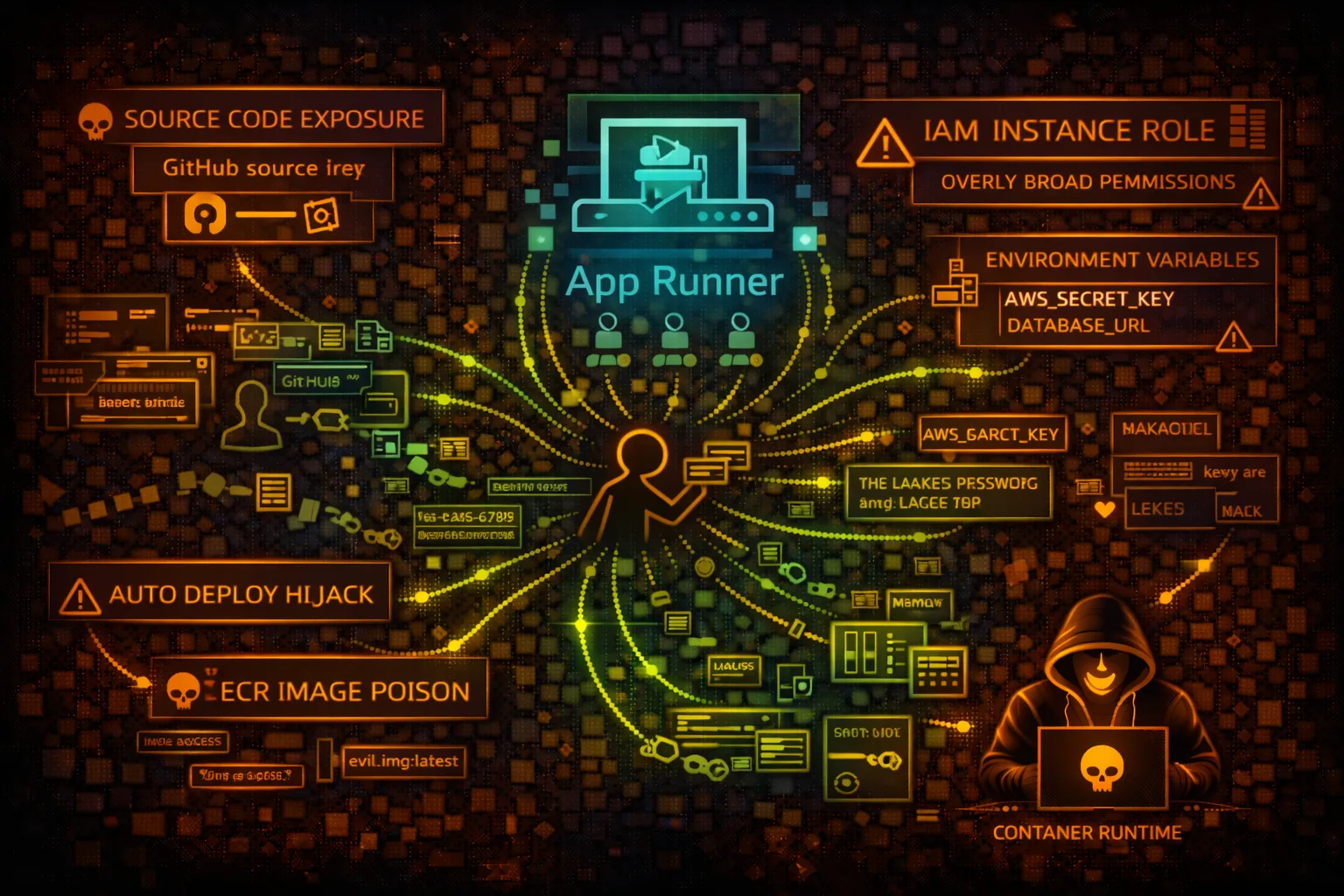
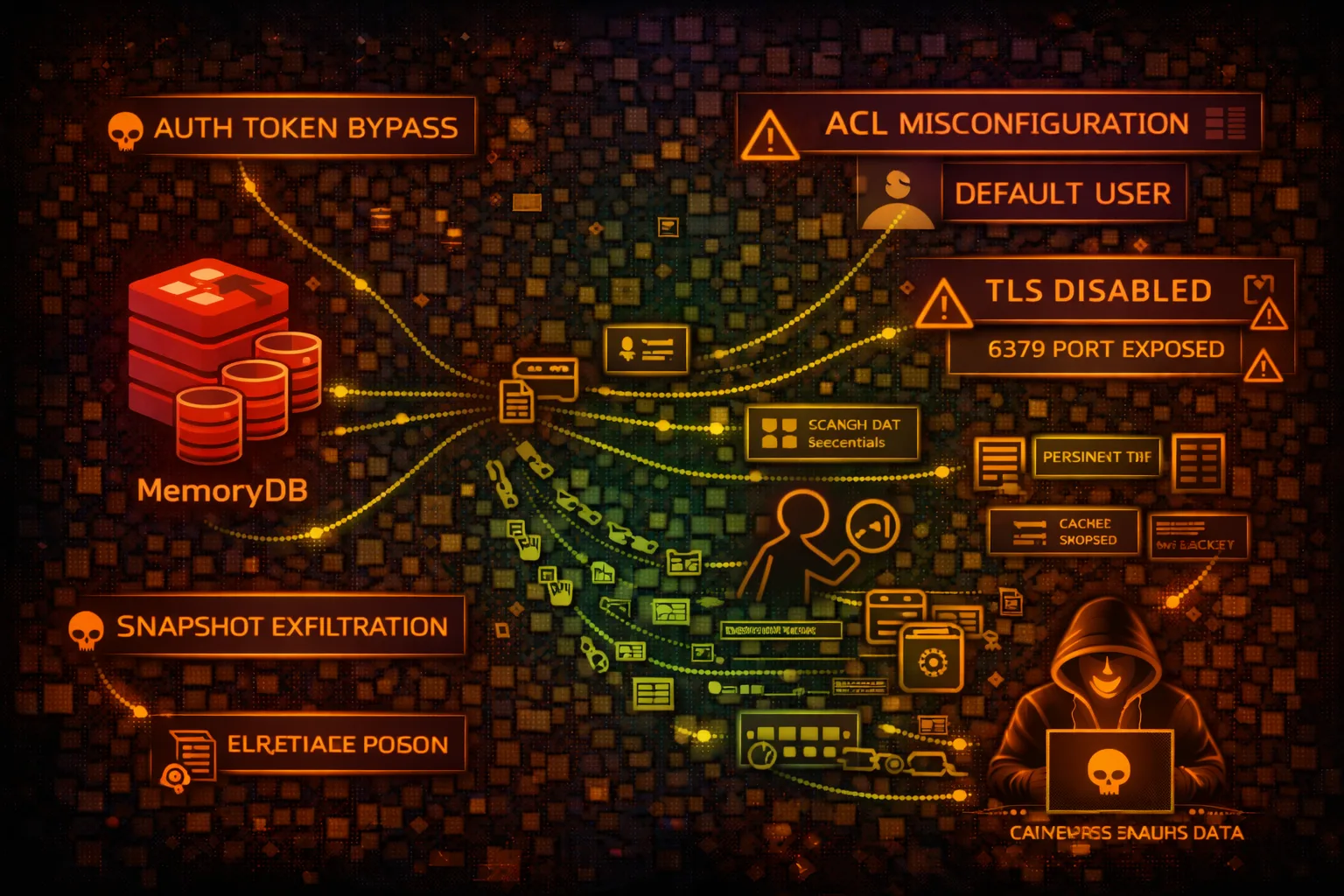
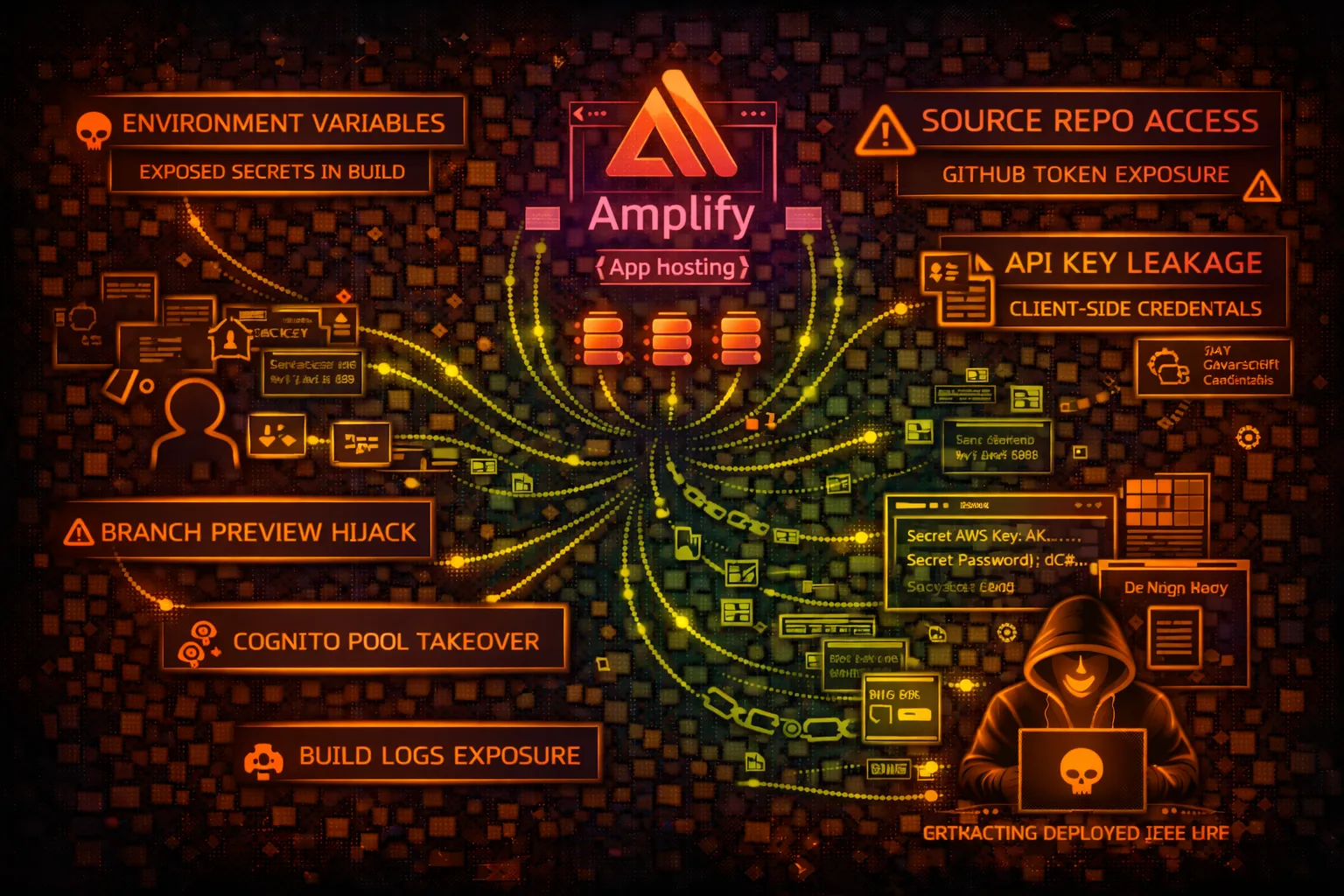
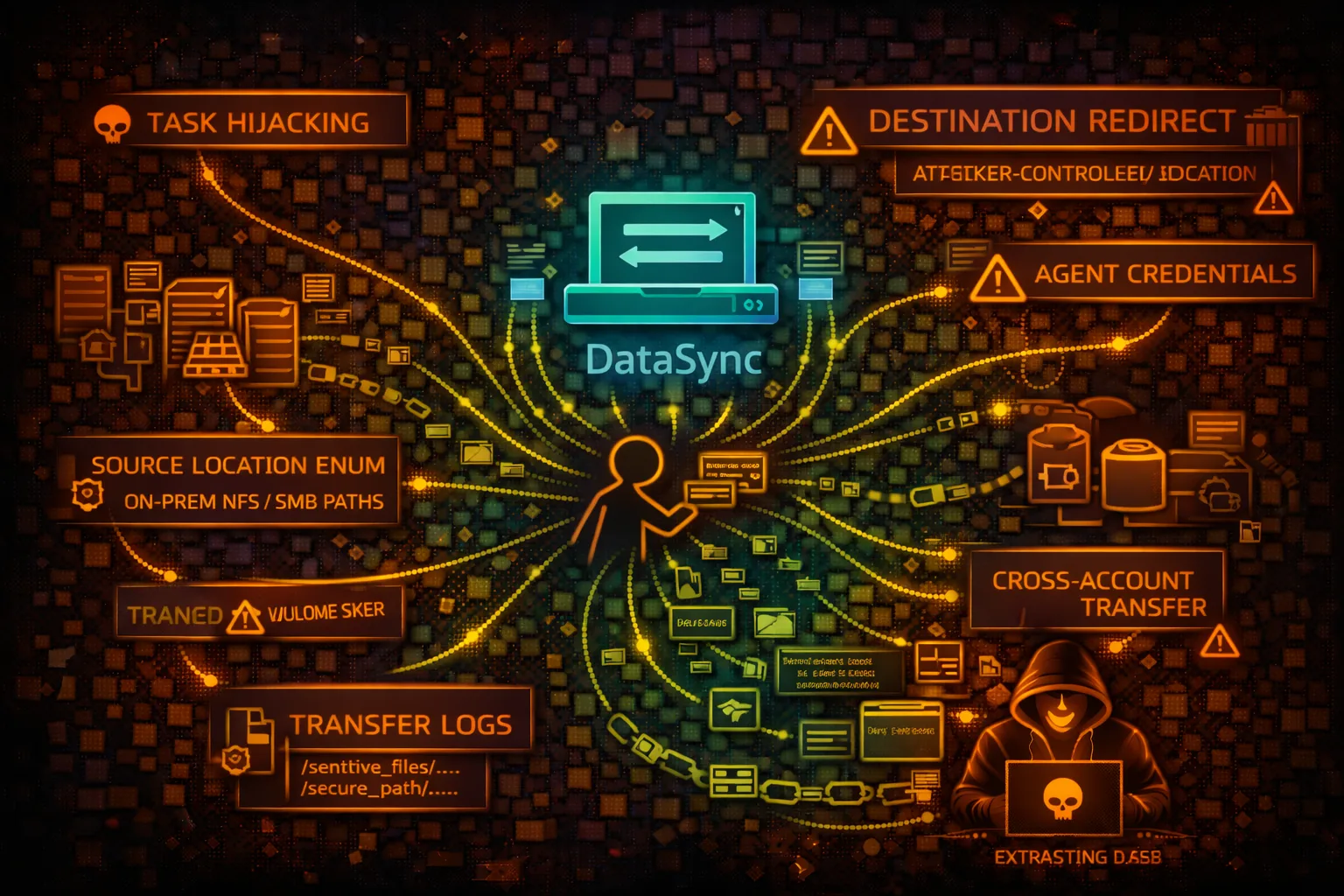
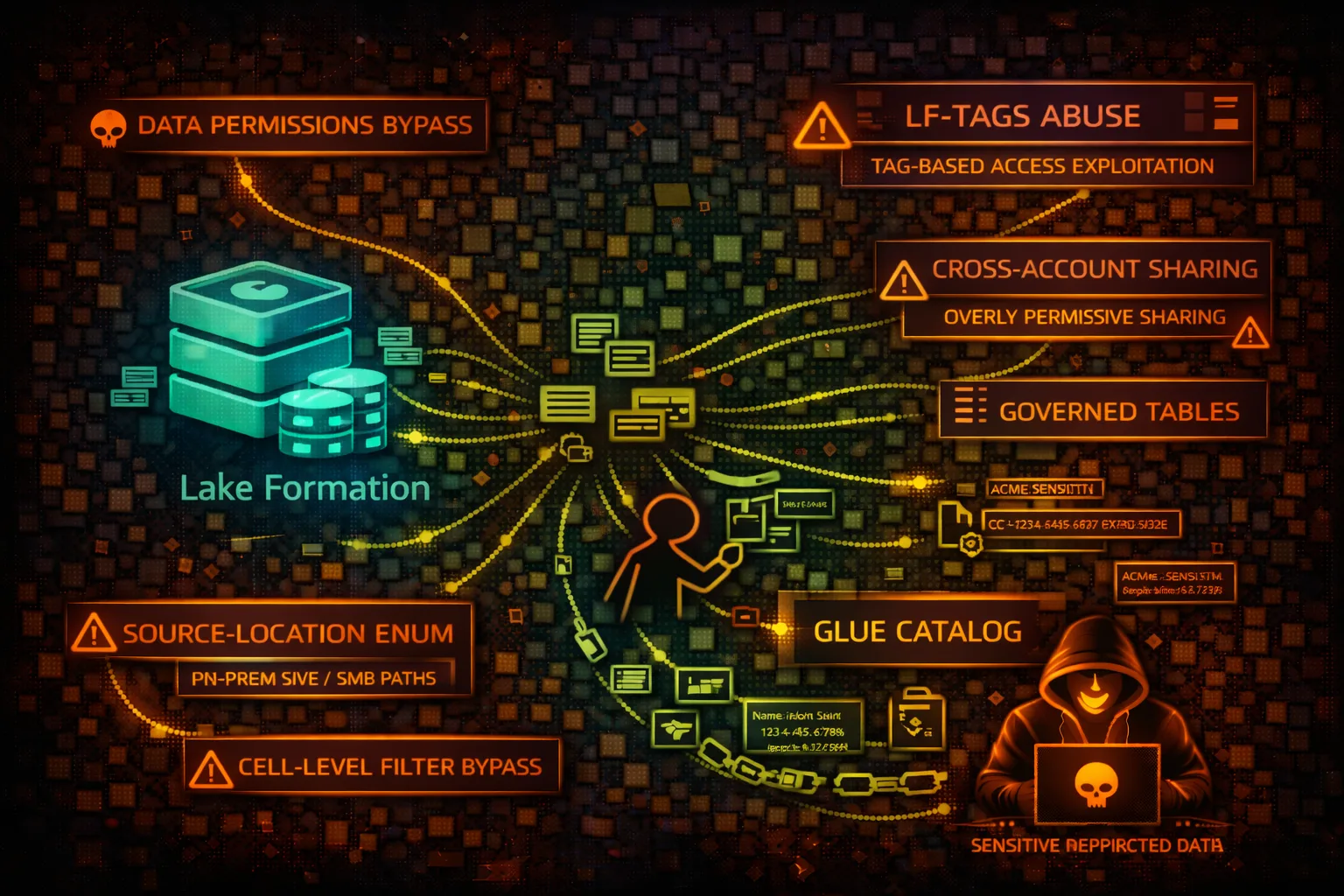
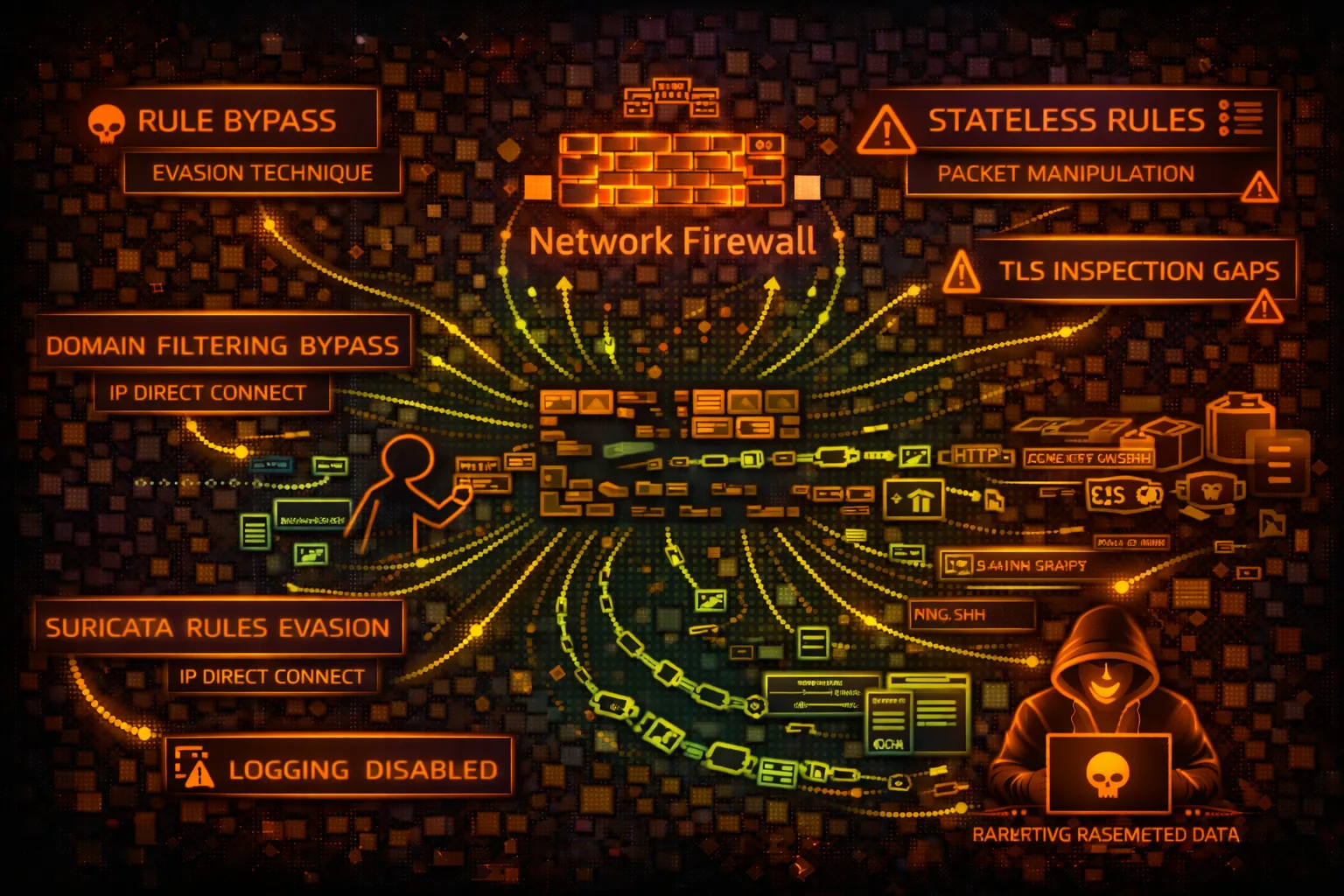
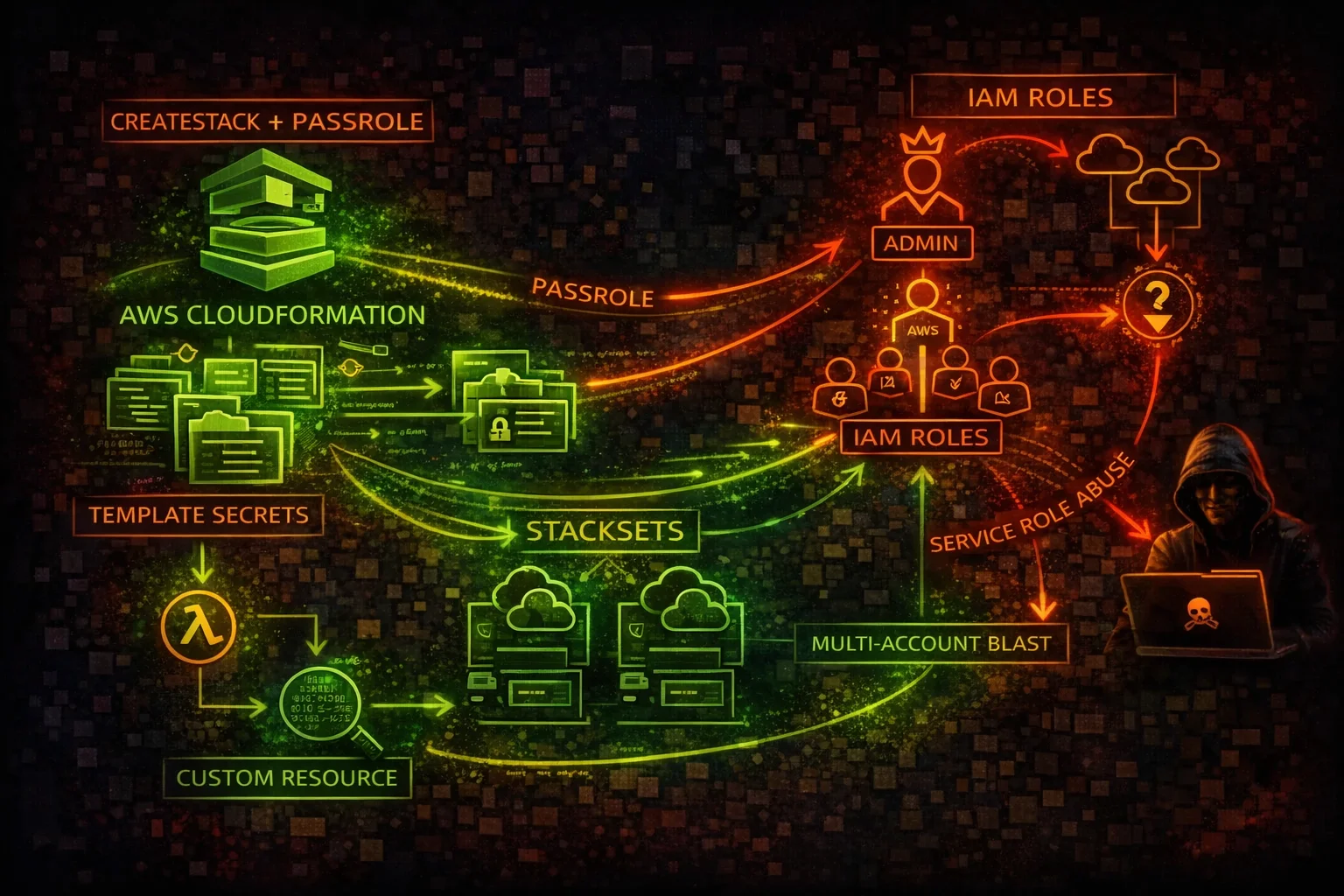
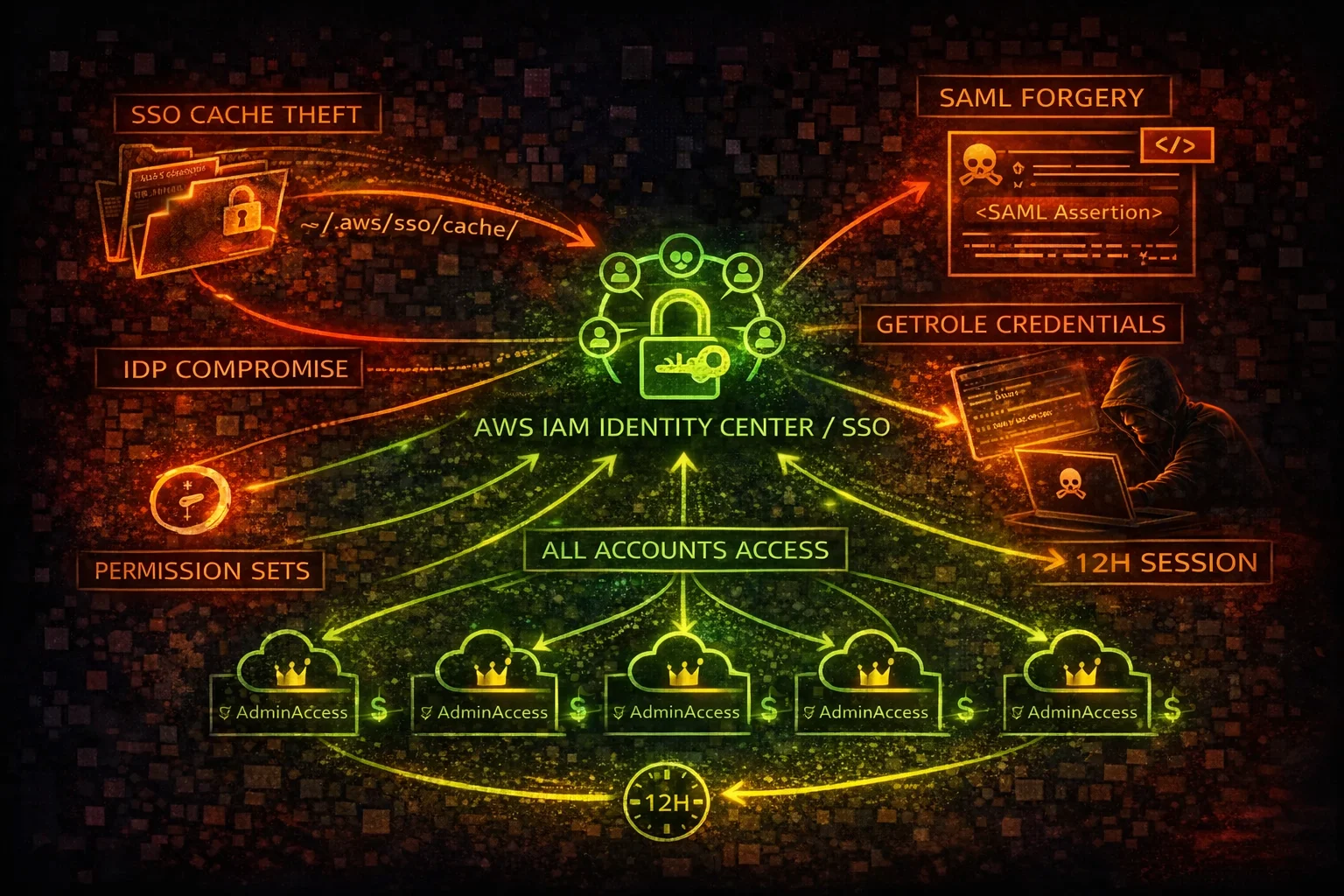
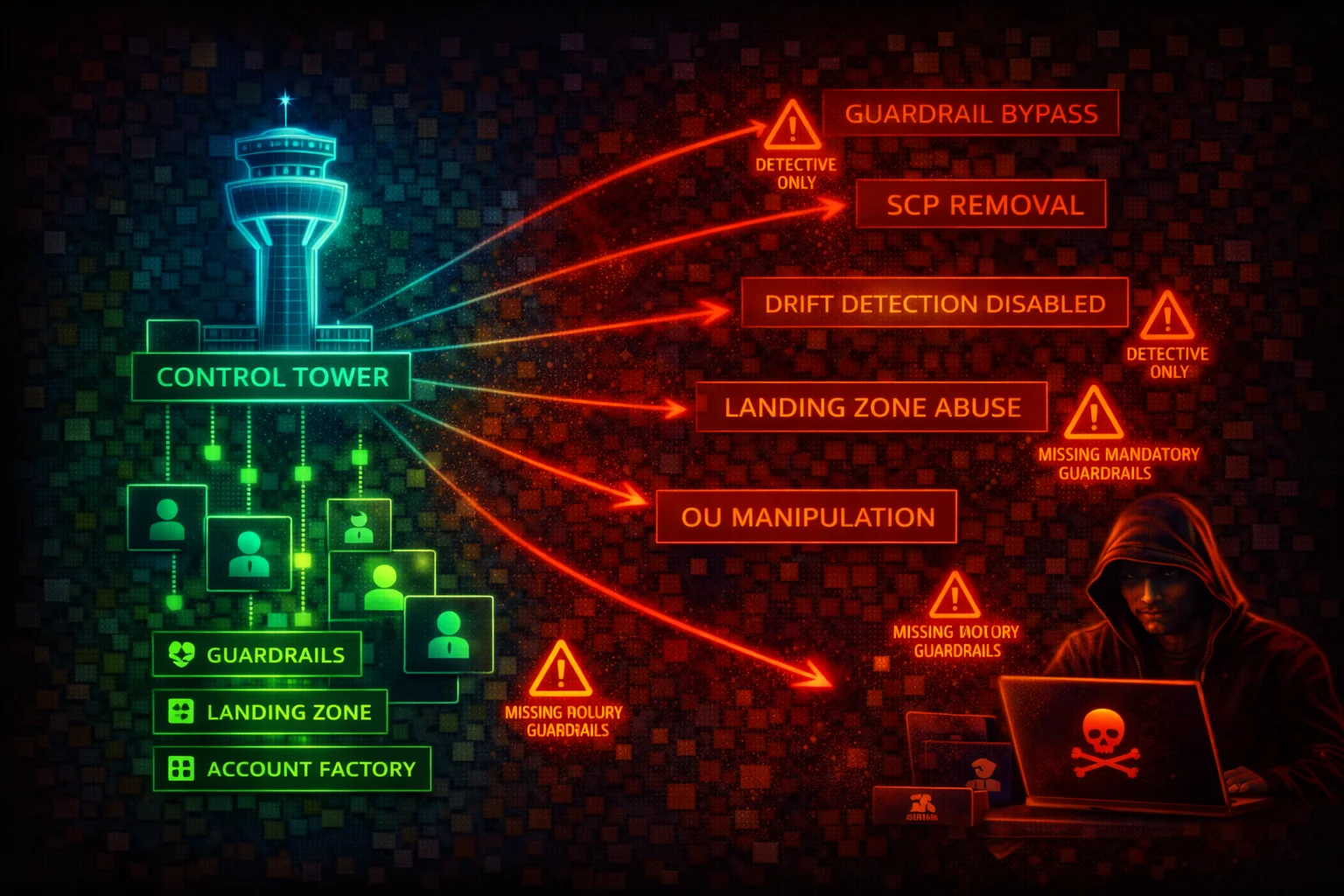
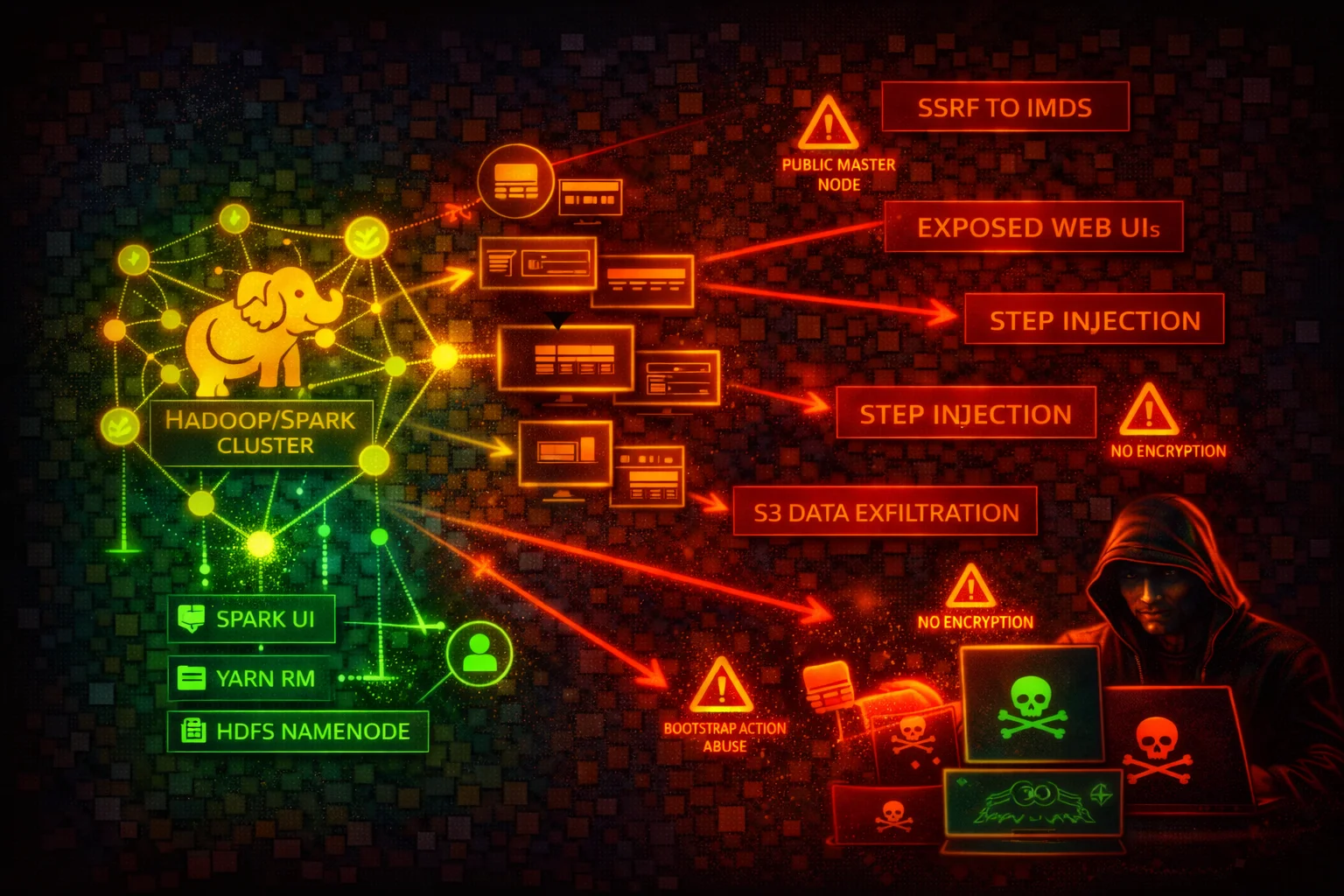
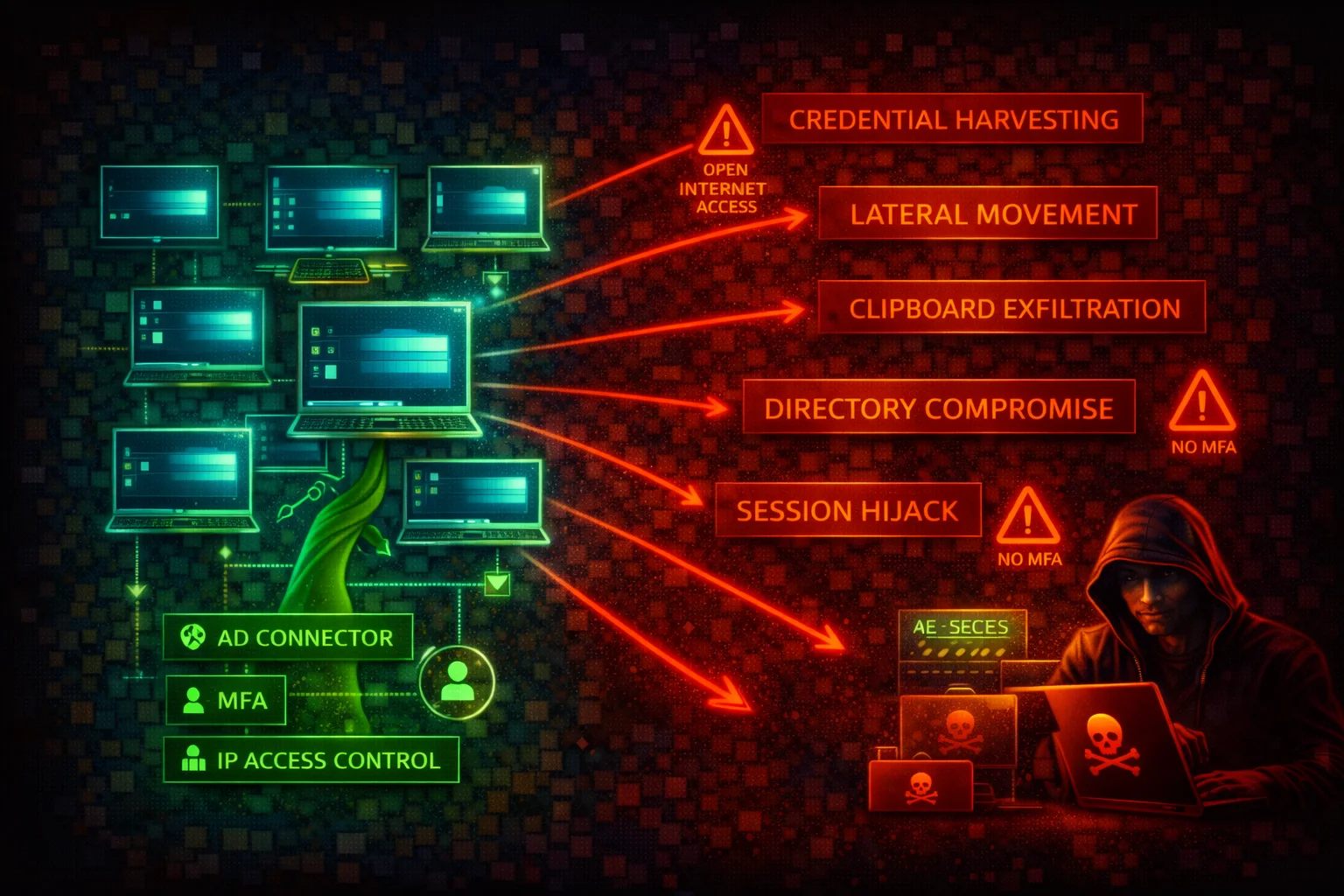
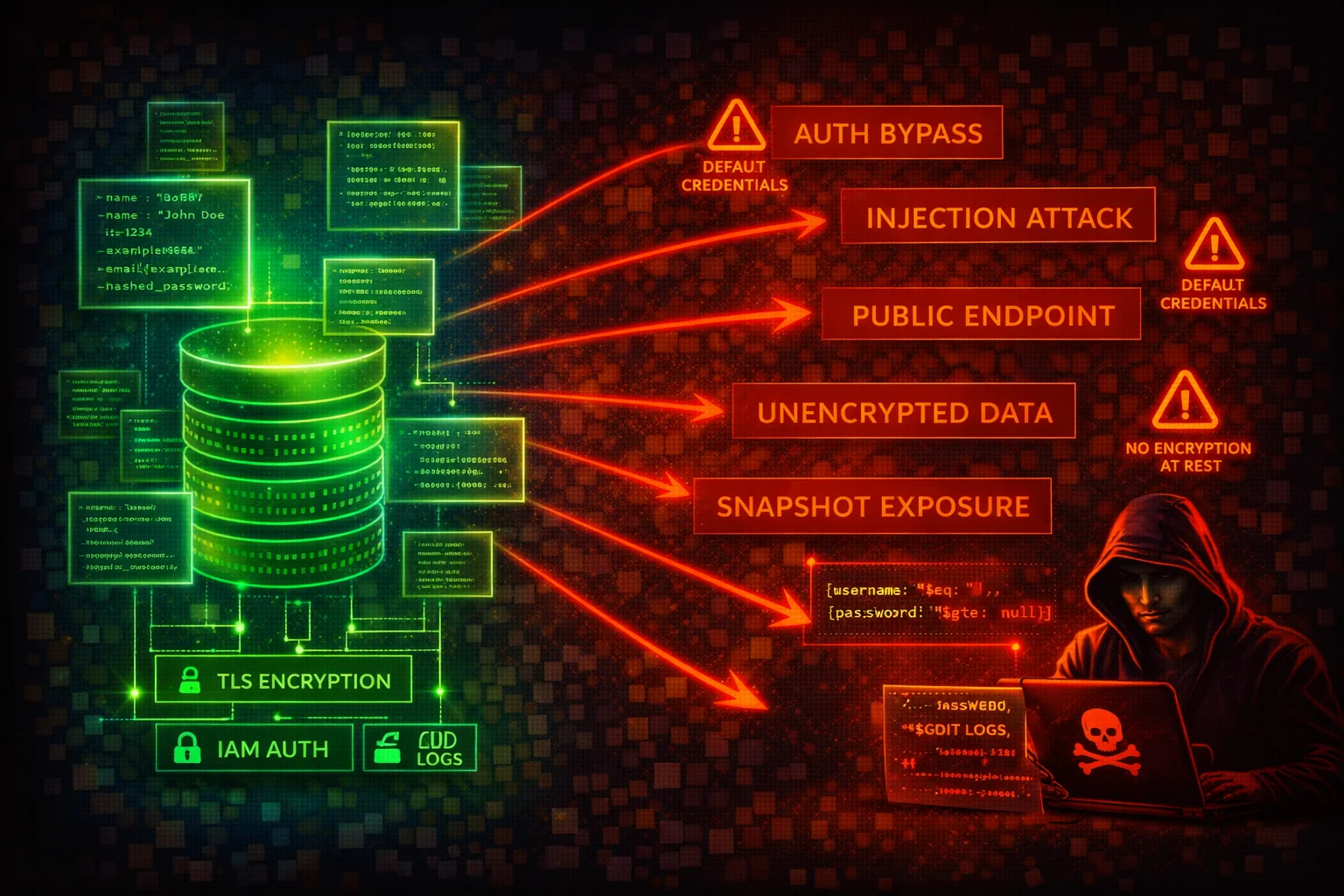
Free, comprehensive security reference guides for every major AWS service. Attack vectors, misconfigurations, CLI commands, and detection indicators.
By Toc Consulting - AWS Security & Cloud Architecture
75 cards found